For more than 30 years, organizations have had their hands full protecting their data, intellectual property, and Information Technology from cyber threats, securing the bits and bytes crucial for business continuity. More recently, OT and infrastructure – vital, large-scale industrial assets that used to be air-gapped but are now exposed to dangerous threat actors – have become the focus of the most sophisticated attacks. Adding into the mix the complex technological advancements from the rapid emergence of IoT, and we are suddenly witnessing the exponential growth of attack vectors.
Merging Domains
The benefits of combining all three domains into one comprehensive OT cyber security solution are as obvious as they are vital: Smart sensors and other IoT devices spread across production lines, generating and consuming crucial operational and business data. As a result, industrial environments increasingly rely on the integration of automation, communications, and data. The world is now at the zenith of the three-way convergence of IT, OT, and IIoT solutions.
Hackers Creeping Across Domains
Where OT assets used to be isolated from the IT part of the business, they are now converged with it – and the cyber attackers are noticing. Their lateral movements now enable them to jump from the shipping department to the factory floor and, once there, onto sensors, machines, and entire industrial networks, disrupting production and holding enormous production facilities to ransom.
We invite you to watch our joint webinar with CYE on demand now to find out how your organization can join the international vanguard against cyber threats across the world’s critical infrastructure.
Unified Approach that Sees and Protects All Assets
With OT, IT, and IoT rapidly converging, organizations can no longer seek protection in the implementation of disparate cybersecurity strategies in each of the three separate domains. They must adopt a unified OT cyber security strategy with an effective, comprehensive, and affordable solution. It’s imperative that the solution will protect ALL their assets and data against cyber threats that can arise and attack them from anywhere in their converged operations.
The benefits of combining all three domains into one comprehensive cybersecurity solution are as obvious as they are vital:
- Single pane of glass to continuously monitor the complete security posture
- Proactively quantify risks and identify exposures across all IT, OT, Industrial IoT environments
- Obtain asset inventories of all OT/IT/IIoT assets aligned with business processes
- Secure the digital transformation to Industry 4.0
- Expand the coverage of security visibility to areas that are currently in a blind spot
- Support the growing body of standards and simplify compliance processes
- Build long-term cybersecurity best practices via the combination of technology and services
End-to-End Protection for Converged IT/OT/IoT Environments
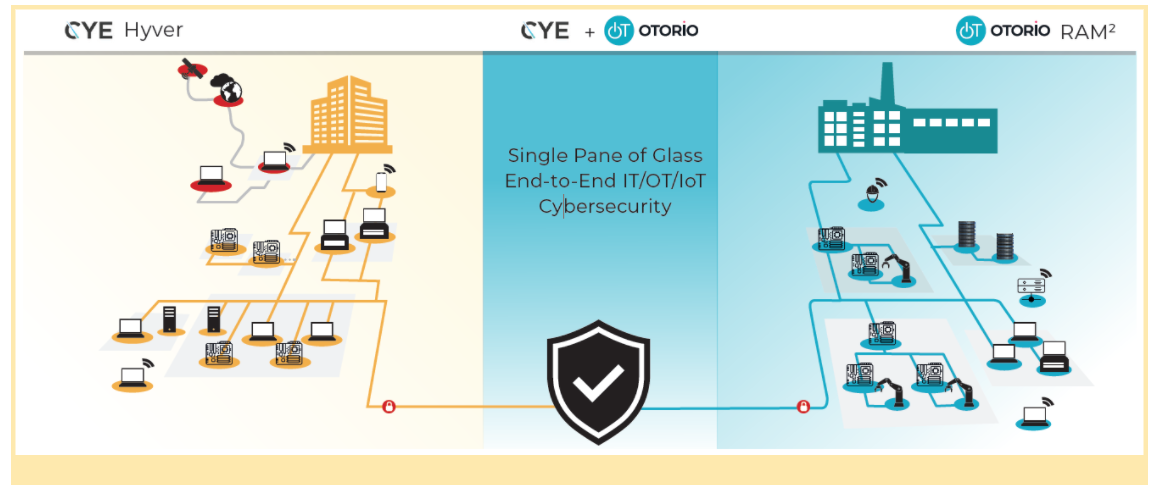
OTORIO's cutting-edge, OT security solution provides the highest level OT cyber protection, and CYE, a trusted IT cybersecurity advisor to medium-sized and Fortune 500 companies, have come together to deliver the first unified solution for monitoring and managing cybersecurity across the entire gamut of converged IT, OT, and IoT.
From a single pane of glass, organizations can view and understand their total security posture and protect their assets all the way from the bits flowing across their IT networks to the protocols that drive the machines on the factory floor.
CYE’s leading IT cybersecurity solution, Hyver™, provides full visibility of attack routes in enterprise networks, translating technical risks into business risks by correlating asset value, severity of vulnerabilities, and threat-actor activity.
OTORIO’s RAM2 delivers unique, proactive risk management that grants visibility and simplified cybersecurity management over all OT and IoT assets, and IT devices in the operational network, correlating multiple security events into focused insights, and prioritizing risks by their impact on operational processes.
Integrated together, Hyver and RAM2 unify and extend effective cybersecurity across the entire organization and ALL of its assets.
Pre-Breach Precautions and Post-Breach Detection and Protection
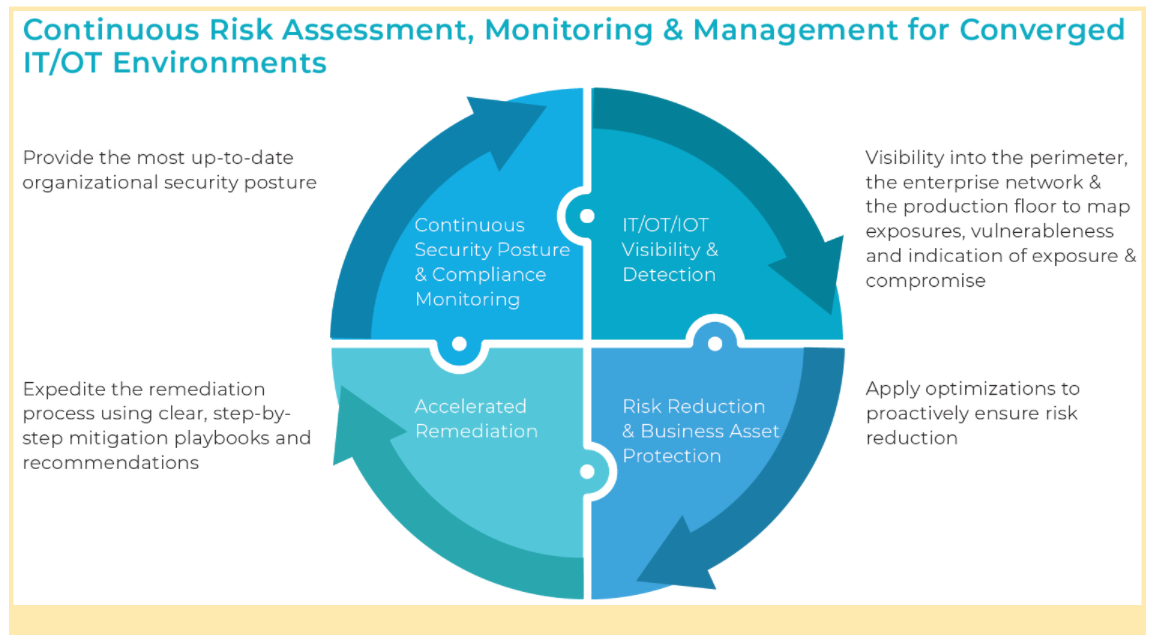
The unified solution takes full advantage of RAM2’s continuous monitoring of the production-floor asset inventory, OT vulnerabilities, and specialized mitigation steps along with its passive monitoring, active querying, and orchestration of security and industrial data sources within the OT environment. OTORIO RAM2 generates Indicators of Exposure (IOE) and Indications of Compromise (IOC) and correlates them to identify suspicious attack patterns in the OT environment even before an actual breach is encountered.
CYE Hyver provides similar capabilities on the IT side. In addition, it identifies needed optimizations for risk reduction across the organization’s networks and endpoints. The joint solution improves the ability to identify gaps and exposures before they can be exploited, while improving early detection of breach attempts and ongoing attacks, and rapid mitigation no matter where the attack started and where it has spread.
Prioritized Mitigation and Remediation
The unified solution provides actionable mitigation plans based on the prioritization of attack routes and the calculation of the potential impact of each risk to production and business continuity. This helps organizations to quickly remove threats and mitigate breaches while optimizing resource allocation and adhering to budget and operational constraints.
Security Posture and Compliance Monitoring
CYE Hyver’s risk assessment and optimized mitigation plan helps organizations maintain compliance with IT regulatory and industrial standards. It is further enhanced by OTORIO RAM2’s asset, process, site and multisite-level security configurations and compliance checks according to common and emerging industrial security standards such as IEC 62443.
The Power of One
OT, IT, and IoT are rapidly converging. All three domains are under increasing threats that steal vital information, halt production, and even put human lives at risk. The era of treating their cybersecurity needs separately is rapidly coming to a close. The benefits of combining all three into one comprehensive cybersecurity solution are immediate and crucial for Industry 4.0.
OTORIO and CYE are delivering these benefits now.
Recent Posts